Linux, Mac OS, Unix: file permissions and user classes
17 minutes
Tip using Ko-fi or Buy Me a Coffee
Using the Linux terminal (command line) I am going to explain in thorough detail the mysteries that are the Linux system file permissions for the uninitiated. I will be using Ubuntu Linux 12.04 LTS but most of what is covered should be applicable for any POSIX compatible Linux, Mac OS or Unix environment.
If this walkthrough tutorial does not meet your needs I have provided some links to other articles on this subject at the end of the piece.
For this article I will interchange the term “file or directory” for the word “item”.
List -long
If you have ready access to a Linux terminal enter the following commands.
cd /boot
ls
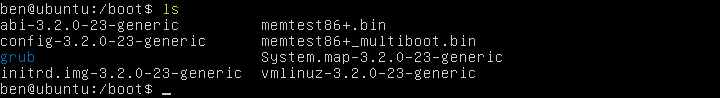
A list similar to the image above should be outputted. The ls command lists the content of the current directory. You can discover the list command’s many options and parameters in the Ubuntu manual pages. http://manpages.ubuntu.com/manpages/precise/man1/ls.1.html.
ls -l
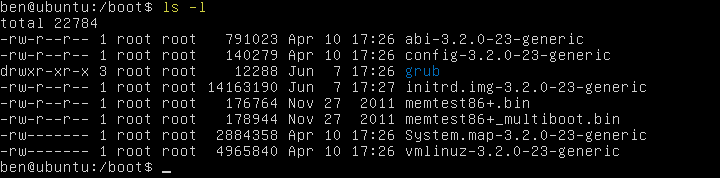
By using the -l (lowercase L) option with the list command we display the content in a long and more detail format.
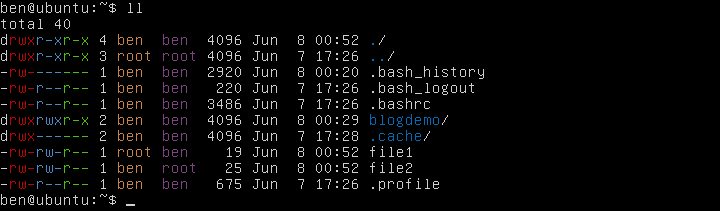
ll
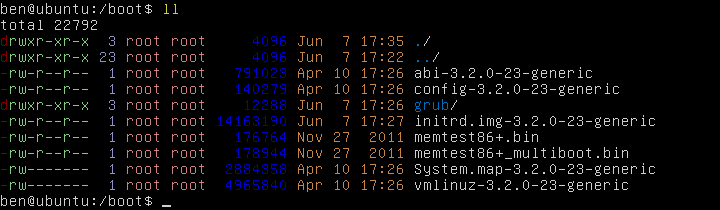
The ll (lowercase LL) command is available on many Linux distributions and is a shortcut that displays identical results to ls -l. For the output above I have colour coded the different columns of item information so I can describe their purpose.
- Red: lists the item type
- Green: lists the item’s permissions.
- Purple: lists the total number of hard links pointing to the item.
- Pink: lists the item’s user (which is the owner) and its applied group.
- Blue: lists the size of the item in bytes.
- Orange/Brown: lists the date and time the item was last modified.
- White: list the item name though some items in this column may have alternative colourings.
Item type
The item type can be broken down into 6 values.
–(dash) is a standard file.dis a standard directory.l(lowercase L) is a symbolic link otherwise known as a symlink.pis a named pipe otherwise known as a FIFO (file-in, file-out).bis a block special file.cis a character special file.
Standard Files and Standard Directories
Standard files and standard directories are the bread and butter of your Linux system. Files are documents of data. While a directory is a container which can hold multiple files as well as additional directories which are called subdirectories.
Symbolic Link
A symbolic or a soft link is a pointer to another file or directory. This enables you to have an item (called a target) in one location and one or more links pointing to to the target located elsewhere on the file system. These pointers can open, read and write to the target. Here is a little demo.
mkdir ~/blogdemo
cd ~/blogdemo/
echo "Hello world" >> hi
cat hi
ln -s hi readme
cat readme
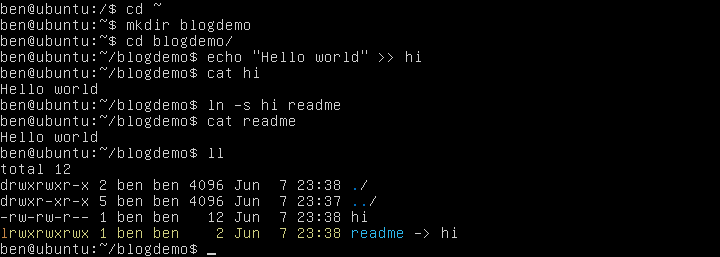
Okay so what I just did was to create a new text file called hi and then display it. I then created a symbolic link named readme that pointed to the new text file. And finally I displayed onscreen the content of the readme link.
The mkdir command creates a new directory.
echo text prints the text contained within the quotes.
>> pipes (moves) the printed text into the file named hi.
cat displays the content of the the file hi onscreen.
ln -s <target> <link name> creates a symbolic link to the target.
You can see with the output of the ll (lowercase LL) command the yellow highlighted line is a symbolic link. The item type is listed with a l (lowercase L) while the item name readme has an arrow -> pointing to its target, which is the text file named hi.
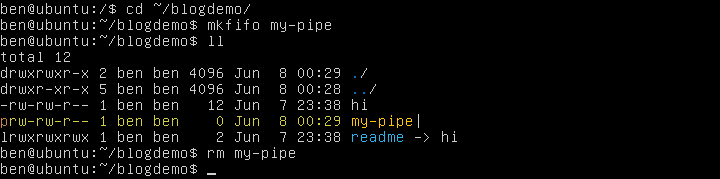
Named Pipes
While rare in usage, named pipes or FIFO are objects that allow you to feed the data output of a source program to the data input of destination program. Below will create, list and delete a pipe but its proper use is beyond this article.
The IBM developerWorks Learn Linux, 101: Steams, Pipes, and Redirects article covers pipes in proper detail. http://www.ibm.com/developerworks/linux/library/l-lpic1-v3-103-4/
mkdir ~/blogdemo
cd ~/blogdemo/
mkfifo my-pipe
ll
rm my-pipe
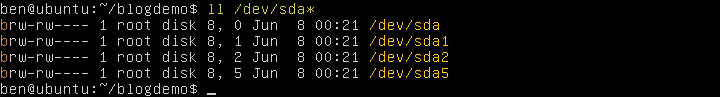
Block and Character Special Files
In most situations you will not need to worry about either one of these file types. Block special files and character special files are unique in that they can receive and generate data. They are most commonly used by files that permit terminal and file system interactions with a piece of physical hardware attached to the computer. Block special files can handle multiple characters at once while character special files only handle single characters. Below is an example of some block special files that can be used to interact with the computer’s SATA hard disks.
ll /dev/sda*
Permissions
From here I will cover file-directory permissions and classes. The commands below will setup a couple of demonstration files in your home (~) directory.
cd ~/blogdemo/
echo "I am a filler file" > file1
echo "I am another filler file" > file2
chown ben file1
sudo chown :root file2
ll
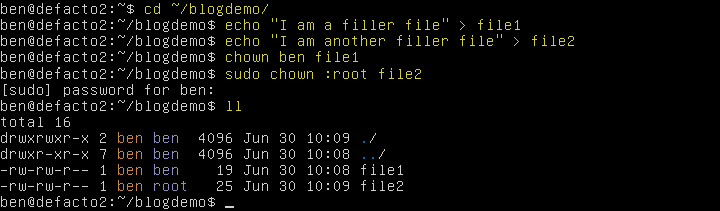
Owner and Groups
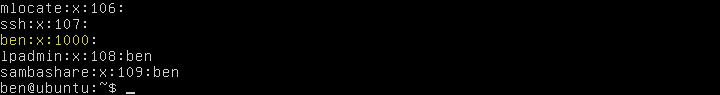
The first thing you should look at in the previous screenshot is the orange/brown column which contains the owners of the items. The purple column that sits next to it lists the groups assigned to the items.
A group is a collection of different user accounts associated together under a common name. A user account can either have no group assigned, a single primary group assigned or a primary group with multiple secondary groups assigned.
A list of your Linux users are stored in the /etc/passwd file.
nano /etc/passwd
The groups are stored in the /etc/group file.
nano /etc/group
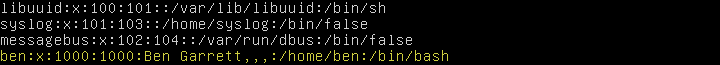
The Ubuntu manual pages has more on the content and format of these passwd and group files.
http://manpages.ubuntu.com/manpages/precise/man5/passwd.5.html http://manpages.ubuntu.com/manpages/precise/man5/group.5.html
Classes and Permissions
The permissions comprise of 9 cryptic columns of data which are individually called bits and they can be separated into 3 classes.
The first set of 3 columns (coloured in red) belong to the user class which is the owner of the item. Remember the owner is listed in the orange/brown coloured column.
The second set of 3 columns (coloured in blue) belong to the group assigned class, that group is listed in the purple coloured column.
While the third set of 3 columns (coloured in green) belong to the other class. These are users who do not fall into the previous two classes.
Each of these classes with their 3 individual columns of bits adhere to an identical format that is set to one of these six combinations.
wrx, wr-, w–, -rx,-r-,–x
w states the write permission is granted
r states the read permission is granted
x states the execute permission is granted
– states the permission is denied and acts as the negative bit character for w, r and x.
So for example wrx means write, read and execute has been granted. While -r- means only read has been granted and write and execute have been denied.
The function of these permission bits is different depending on whether the item is a directory or a file.
File Permission Bits
w is the write bit, it allows the file to be modified, renamed and deleted.
r is the read bit, it allows the content of a file to be viewed.
x is the execute bit, it registers the file as a program and allows it to be run.
Directory Permission Bits
w is the write bit, it allows the directory to be renamed or deleted plus it allows new files and subdirectories to be created within.
r is the read bit, it allows the content of the directory to be listed using commands such as ls or ll.
x is the execute bit, it allows access into the directory using commands such as cd. If the execute bit has been denied (–) access to all subdirectories and files within this directory will be barred. This denied bit overrides both the directory’s write bit and read bit permissions.
Let’s take a closer look at the file file1

The orange/brown text tells us that this file is owned by the user root.
The purple text shows that the file is assigned to the group named ben.
Now looking at the permissions.
The red set of bits are the permissions for the user which is another name for the owner. This owner root can read and write to (rename, delete or modify) this file. These permissions nullify any of the lesser class permissions that might also match the owner.
The blue set of bits are for the group ben which is assigned to this file. Users assigned to ben can read and write to (rename, delete or modify) this file.
The green set of bits are for others who are users that do not fit the previous two classes. They can only read this file.
Let’s take a closer look at the directory blogdemo/

Firstly the orange/brown text tells us this directory is owned by the user ben.
The purple text states that the directory has been assigned to the group ben. When a new user account is created a default group under the same name is also generated. This group is then assigned to the user and is used as their primary group.
The red set of bits is for the user which is another name for the owner. The owner ben has write (rename, delete, add new files or subdirectories with), read (list content) and execute (access into the directory) permissions.
The blue set of bits is for the group assigned to this directory which is named ben. Users who are assigned to the group ben have write (rename, delete, add new files or subdirectories with), read (list content) and execute (access into the directory) permissions.
Please note that ben is the owner of this directory, he is also assigned to the group ben. As there is a conflict the (lesser) group permissions are nullified for him as the user (owner) permission bits take precedence.
The green set of bits are for other and they are the users that do not fit in the previous two classes. They have permission to read (list content) and execute (access into the directory).
Change owner (chown) or change modification (chmod)
When you create a new directory or a new file that item’s ownership is automatically set to you. Your primary group is also assigned to the item. When you create an item while using the sudo (superuser do) command ownership is given to root and the group is assigned to root.
cd ~/blogdemo
mkdir bens_stuff
sudo mkdir roots_stuff
ll
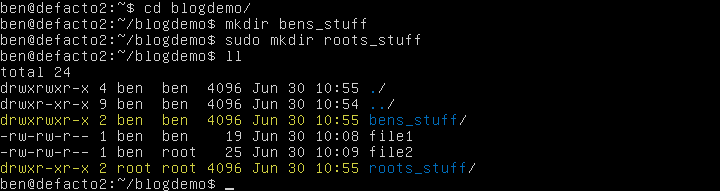
To change ownership or group assignment of an item you can use the chown command
To change the owner.
chown <user name> <item>
To change the group assignment apply a semicolon before the group name.
chown :<group name> <item>
You can change both the owner and group assignment together and also apply the changes to multiple items at once.
chown <user name>:<group name> <item1> <item2> <item3>
In Ubuntu you can obtain a list of users and the list of groups by running the following.
nano /etc/passwd
nano /etc/group
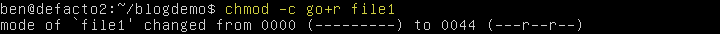
To change the item permissions you can use the chmod command
chmod <option> <mode> <item>
chmod -c will verbosely display all changes to each item you make which is useful in checking for mistakes.
The is broken down into three sets of requirements that we will isolate with squared brackets.
chmod -c [class][sign][permission] <item>
The [class] set are the user classes of the item you wish to modify and it permits the following options.
[ugoa] u user (owner), g group, o other, a all.
You can apply more than one class at a time, for example the following would make changes to both the item’s user and the group classes.
chmod -c ug[sign][permission] <item>
While the all (a) class is a shortcut that combines the user (u), group (g) and other (o) classes. The two commands below have identical functionality.
chmod -c a[sign][permission] <item>
chmod -c ugo[sign][permission] <item>
The second set of input [sign] involves mathematical signs which represent the method we want to apply.
[-+=] + add, – remove, = set (replace)
+ add will insert [permission] to the item class.
– remove will delete [permission] from the item class.
= set will delete all existing permissions from the class and replace them with [permission].
The following would add [permission] to item’s user (owner) and group classes.
chmod -c ug+[permission] <item>
The following would remove [permission] from the item’s user, group and other classes.
chmod -c ugo-[permission] <item>
The following would replace all permissions with [permission] for the item’s user, group and other classes.
chmod -c a=[permission] <item>
Finally the third set of input [permission] involves the types of access you wish to grant. These attributes are commonly referred to as bits. The word ‘bits’ is a contraction of the term “binary digit” which describes a two state representation of data ie enabled / disabled.
[rwxX] r read, w write, x execute, X safe execute.
Remember I mentioned earlier in File Permission Bits and Directory Permission Bits that the execute bit has different functions depending on if it is applied to a directory or a file.
The safe execute (X) bit is recommended for use over the execute (x) bit as it does not apply the potentially dangerous execute bit to files and will only set it to directories. This is convenient when you mass-apply permissions to the content of a directory.
There are a couple of additional permission bits that in general can be ignored unless specifically needed.
[st] s set user/group identity, t sticky
The set user/group identity (s) bit can only be used with the user (owner) and group classes but due to insecurities this functionality is ignored on many Linux distributions including Ubuntu.
When applied to a file the (s) bit grants the other class elevated execute permissions. If the (s) bit is applied to the user class, the other class will have identical execute permissions to those of the owner. The same is true when the (s) bit is applied to the group class except then the other class will temporarily be assigned to the group when executing the file.
When applied to a directory the (s) bit will force any newly created files or directories to inherit the group assignment of the parent directory rather than that of the user creating the item. This functionality is ignored on most Linux distributions and so the (s) bit will probably have no effect.
More detailed information on this bit can be read at http://en.wikipedia.org/wiki/Setuid
Finally the sticky (t) bit is an elevated setting to allow only the item’s owner or a superuser permission (such as root) to delete or rename a directory. This bit is only useful when the other or group classes have the write bit applied to the same directory. The write and sticky bit combination would then allow these classes to create new or delete existing items within the directory but it would block any changes to the directory itself.
So in summary you have the following classes, signs and bits that you can assign to an item.
chmod -c [ugoa][-+=][rwxXst] <item>
Below is a sample of chmod commands and a brief description of their function.
chmod -c go+r <item>
Adds the read permission to the group and other classes.
chmod -c a-w <item>
chmod -c ugo-w <item>
chmod -c -w <item>
All 3 do the same thing and remove the write permission from all classes.
chmod -c go+wt <directory>
Adds the write permission to the group and other classes and assigns the sticky bit.
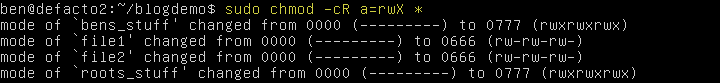
chmod -c a=rwX *
Removes all previous permissions for all classes and assigns read, write and safe execute to all items in the current directory. By using the safe execute bit (X) only directories will be set with an execute bit, the execute bit for files will remain unchanged.
chmod -cR a+rX *
Adds the read and safe execute permission to all classes in the current directory. The -R is a recursive option to mass apply changes to all items contained within the subdirectories. This is potentially dangerous as for example if you accidently ran chmod -R +x / you would grant execute permission to all users for nearly every file on your Linux file system!
chmod -c o= <item>
Will set the other class permission to deny.
Octal Numeric Modifications
While you now have all the information that you need to successfully change and modify directory-file user ownerships and permissions we are not yet finished. Often in Linux walkthroughs or instructions you will encounter a different set of numeric only permissions being used with the chmod command. For example..
chmod 755 <directory>
These numbers are known as octal notation permissions.
Octal numerals are a set of numbers with a base of 8 that use a numeric range of 0 – 7. This is slightly different to the more familiar decimal numerals that use a base of 10 with a numeric range of 0 – 9.
These octal based permissions have 4 specific digits that represent permission bits.
0 represents – which is the denied bit.
1 represents x which is the execute bit.
2 represents w which is the write bit.
4 represents r which is the read bit.
You can sum (add) different numeric values to represent combined bits.
1+2 = 3, represents w-x which are the write and execute bits.
1+4 = 5, represents -rx which are the read and execute bits.
2+4 = 6, represents wr- which are the write and read bits.
1+2+4 = 7, represents wrx which are the write, read and execute bits.
Now chmod requires a 3 digit numeric value between the range of 000 and 777. You cannot supply a single (0-7) or a double digit (00-77) value. As each digit represents a permission assignment for one of the three item classes. The first digit is for the user (owner) class, the middle digit is for the group assignment, while the final digit is for other.
So an octal permission value of 750 is..
7 = user (owner) class, write (2), read (4) and execute (1) bits.
5 = group class, read (4) and execute (1) bits.
0 = other class, the denied (0) bit.
Now hopefully these octal numbers start to make a bit more sense. But a word of warning the use of octal numbers will always overwrite any preexisting bit assignments for all classes. It is a use case shortcut and is not a replacement for adding or removing individual bits.
chmod -c 000 <item>
or in text
chmod -c a= <item>
This removes all permissions to the item.
chmod -c 755 <directory>
or in text
chmod -c u=wrx <directory>
chmod -c go=rx <directory>
This sets the user (owner) to have write, read and execute. While group and other classes have read and execute.
chmod -c 644 <file>
or in text
chmod -c u=wr <file>
chmod -c go=r <file>
This sets the user (owner) to have write and read permissions while the group and other classes have read only.
Congratulations that is the Linux and Unix file permissions and user classes in a nutshell. I hope it has not be too grueling and please feel free comment or ask any questions. Alternative articles on this subject can be found at the following links.
Ubuntu Community Pages: File Permissions https://help.ubuntu.com/community/FilePermissions
Zzee Linux Permissions Help http://www.zzee.com/solutions/linux-permissions.shtml
Mac-Terminal: Manage permission of files and folders in the Terminal for Mac OS X http://www.mac-terminal.com/files-and-folders/permissions/
Written by Ben Garrett
